kubernetes tools
Abstract
Some nice tools to interact with kubernetes. One I’m using daily is k9s.
Monitoring
k9s
K9s is a terminal based UI to interact with your Kubernetes clusters. The aim of this project is to make it easier to navigate, observe and manage your deployed applications in the wild. K9s continually watches Kubernetes for changes and offers subsequent commands to interact with your observed resources.
Link : https://github.com/derailed/k9s
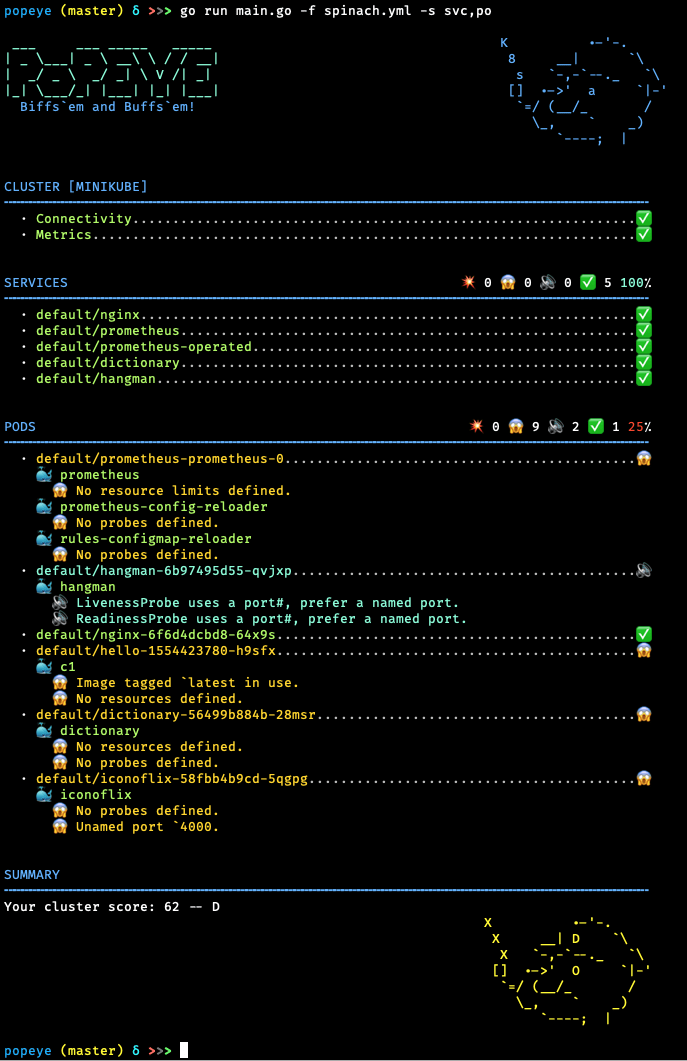
popeye
Popeye is a utility that scans live Kubernetes cluster and reports potential issues with deployed resources and configurations. It sanitizes your cluster based on what’s deployed and not what’s sitting on disk.
Link : https://github.com/derailed/popeye
Package manager
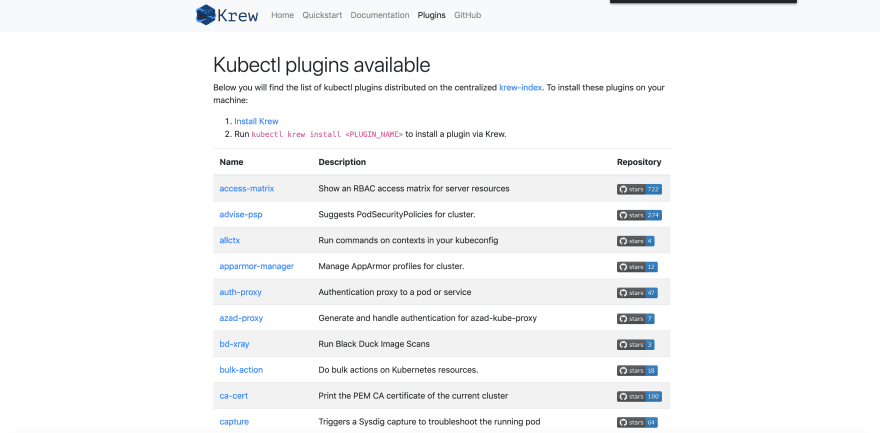
krew
Krew is a tool that makes it easy to use kubectl plugins. Krew helps you discover plugins, install and manage them on your machine. It is similar to tools like apt, dnf or brew. Today, over 100 kubectl plugins are available on Krew.
Link : https://github.com/kubernetes-sigs/krew
Plugins
kubectx + kubens
kubectx helps you switch between clusters back and forth:
kubens helps you switch between Kubernetes namespaces smoothly:
Link : https://github.com/ahmetb/kubectx
kubespy
kubespy is a small tool that makes it easy to observe how Kubernetes resources change in real time, derived from the work we did to make Kubernetes deployments predictable in Pulumi’s CLI. Run kubespy at any point in time, and it will watch and report information about a Kubernetes resource continuously until you kill it.
Link : https://github.com/pulumi/kubespy
kube-score
kube-score is a tool that performs static code analysis of your Kubernetes object definitions.
Link : https://github.com/zegl/kube-score
kubectl-doctor
This plugin is inspired from brew doctor :) It will scan your currently targeted k8s cluster to see if there are anomalies or useful action points that it can report back to you.
This plugin does not change any state or configuration, it merely just scans and gathers information than reports back anomalies in yaml format.
Link : https://github.com/emirozer/kubectl-doctor
ktunnel
Ktunnel is a CLI tool that establishes a reverse tunnel between a kubernetes cluster and your local machine. It lets you expose your machine as a service in the cluster or expose it to a specific deployment
Link : https://github.com/omrikiei/ktunnel
kubectl-tree
A kubectl plugin to explore ownership relationships between Kubernetes objects through ownersReferences on them.
Link : https://github.com/ahmetb/kubectl-tree
Debug/Logs
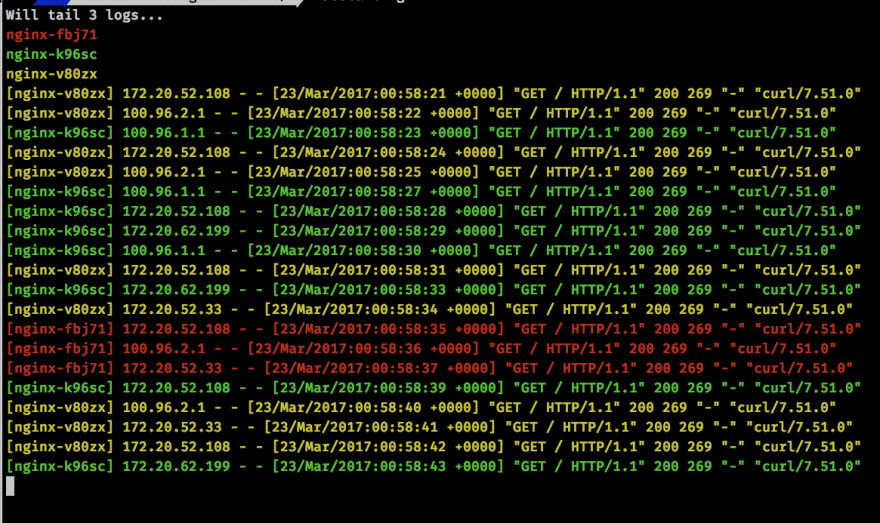
kubetail
Bash script that enables you to aggregate (tail/follow) logs from multiple pods into one stream. This is the same as running “kubectl logs -f ” but for multiple pods.
Link : https://github.com/johanhaleby/kubetail
kubectl-debug
kubectl-debug is an out-of-tree solution for troubleshooting running pods, which allows you to run a new container in running pods for debugging purpose.
Link : https://github.com/aylei/kubectl-debug
stern
Stern allows you to tail multiple pods on Kubernetes and multiple containers within the pod. Each result is color coded for quicker debugging
Link : https://github.com/stern/stern
Alerting
Botkube
BotKube integration with Slack, Mattermost or Microsoft Teams helps you monitor your Kubernetes cluster, debug critical deployments and gives recommendations for standard practices by running checks on the Kubernetes resources. You can also ask BotKube to execute kubectl commands on k8s cluster which helps debugging an application or cluster
Link : https://github.com/infracloudio/botkube
Validation
Polaris
Fairwinds’ Polaris keeps your clusters sailing smoothly. It runs a variety of checks to ensure that Kubernetes pods and controllers are configured using best practices, helping you avoid problems in the future.
Link : https://github.com/FairwindsOps/polaris
goldilocks
Goldilocks is a utility that can help you identify a starting point for resource requests and limits.
Link : https://github.com/FairwindsOps/goldilocks
Helm
reckoner
Command line helper for helm. This utility adds to the functionality of Helm in multiple ways:
- Creates a declarative syntax to manage multiple releases in one place
- Allows installation of charts from a git commit/branch/release
Example :
# course.yml
charts:
nginx-ingress:
namespace: ingress-controllers
version: 1.15.1
values:
controller.ingressClass: "my-ingress-class-name"
Link : https://github.com/FairwindsOps/reckoner
helmfile
Deploy Kubernetes Helm Charts with helmfile
releases:
- name: prom-norbac-ubuntu
namespace: prometheus
chart: stable/prometheus
set:
- name: rbac.create
value: false
helmfile apply
Link : https://github.com/roboll/helmfile
Ship
kubevela
KubeVela is a platform engine to enable designing and shipping applications with minimal effort.
$ vela up -f https://raw.githubusercontent.com/oam-dev/kubevela/master/docs/examples/vela.yaml
Parsing vela.yaml ...
Loading templates ...
Rendering configs for service (testsvc)...
Writing deploy config to (.vela/deploy.yaml)
Applying deploy configs ...
Checking if app has been deployed...
App has not been deployed, creating a new deployment...
✅ App has been deployed 🚀🚀🚀
Port forward: vela port-forward first-vela-app
SSH: vela exec first-vela-app
Logging: vela logs first-vela-app
App status: vela status first-vela-app
Service status: vela status first-vela-app --svc testsvc
Link : https://github.com/oam-dev/kubevela
Helm secrets
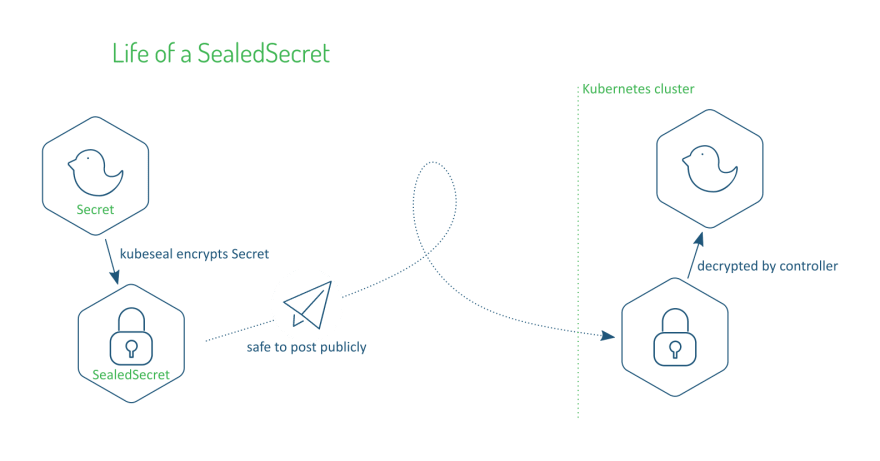
sealed-secrets
In order to store secrets safely in a public or private Git repository, you can use Bitnami’s sealed-secrets controller and encrypt your Kubernetes Secrets into SealedSecrets. The sealed secrets can be decrypted only by the controller running in your cluster and nobody else can obtain the original secret, even if they have access to the Git repository.
# Create a json/yaml-encoded Secret somehow:
# (note use of `--dry-run` - this is just a local file!)
$ echo -n bar | kubectl create secret generic mysecret --dry-run=client --from-file=foo=/dev/stdin -o json >mysecret.json
# This is the important bit:
# (note default format is json!)
$ kubeseal <mysecret.json >mysealedsecret.json
# mysealedsecret.json is safe to upload to github, post to twitter,
# etc. Eventually:
$ kubectl create -f mysealedsecret.json
# Profit!
$ kubectl get secret mysecret
Link : https://github.com/bitnami-labs/sealed-secrets
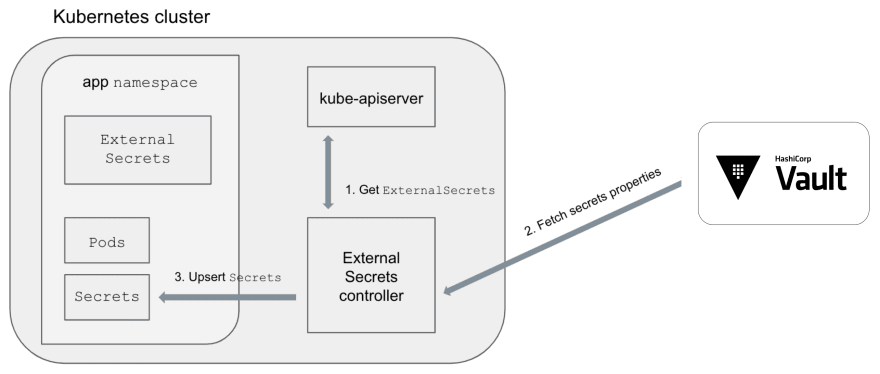
kubernetes-external-secrets
The External Secrets Kubernetes operator reads information from a third party service like AWS Secrets Manager and automatically injects the values as Kubernetes Secrets.